Continuous Monitoring Plan Template
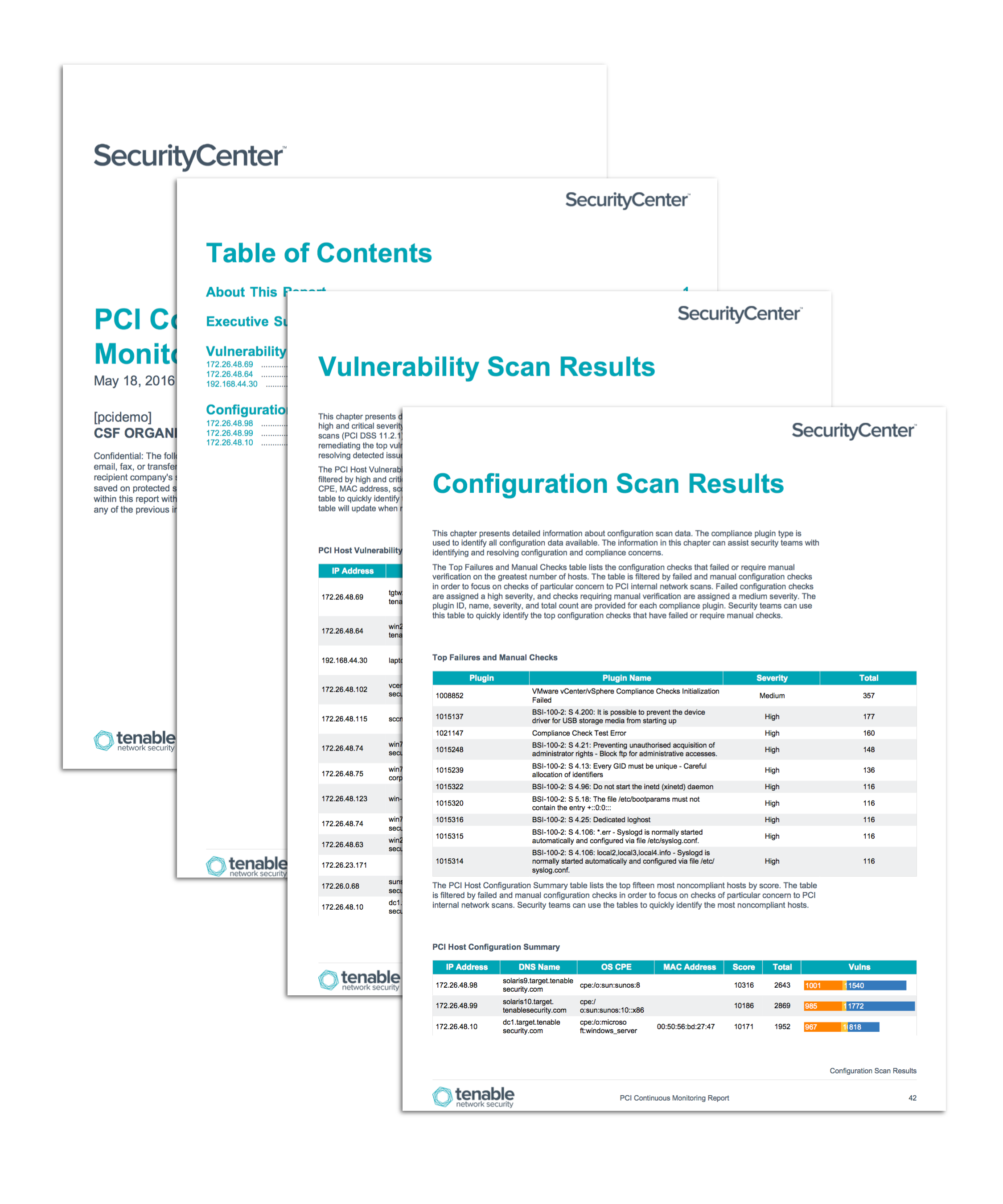
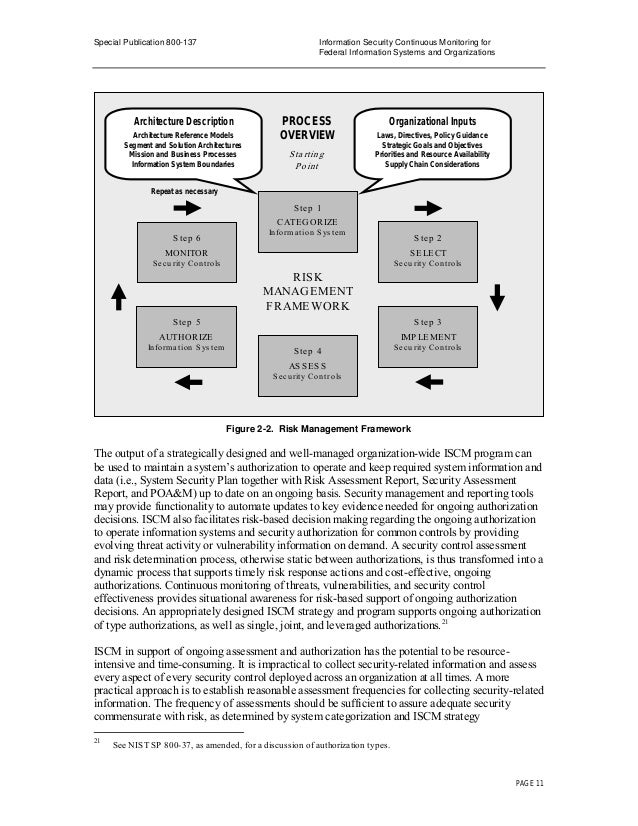
Continuous Monitoring Plan Template - Web this publication describes an approach for the development of information security continuous monitoring (iscm) program. Information security continuous monitoring (iscm) programs provide an understanding of risk tolerance. Web this guideline provides a template for developing a continuous monitoring plan for federal information. Web review and update the monitoring program, revising the continuous monitoring strategy and maturing measurement capabilities to. Ociso will implement continuous monitoring of systems using. Web learn how to plan and implement continuous monitoring activities for your cybersecurity program based on.
Information security continuous monitoring (iscm) programs provide an understanding of risk tolerance. Ociso will implement continuous monitoring of systems using. Web this guideline provides a template for developing a continuous monitoring plan for federal information. Web learn how to plan and implement continuous monitoring activities for your cybersecurity program based on. Web this publication describes an approach for the development of information security continuous monitoring (iscm) program. Web review and update the monitoring program, revising the continuous monitoring strategy and maturing measurement capabilities to.
Web review and update the monitoring program, revising the continuous monitoring strategy and maturing measurement capabilities to. Web learn how to plan and implement continuous monitoring activities for your cybersecurity program based on. Web this publication describes an approach for the development of information security continuous monitoring (iscm) program. Ociso will implement continuous monitoring of systems using. Web this guideline provides a template for developing a continuous monitoring plan for federal information. Information security continuous monitoring (iscm) programs provide an understanding of risk tolerance.
Rmf Continuous Monitoring Plan Template
Information security continuous monitoring (iscm) programs provide an understanding of risk tolerance. Ociso will implement continuous monitoring of systems using. Web this publication describes an approach for the development of information security continuous monitoring (iscm) program. Web learn how to plan and implement continuous monitoring activities for your cybersecurity program based on. Web review and update the monitoring program, revising.
Rmf Continuous Monitoring Plan Template Master of Documents
Web review and update the monitoring program, revising the continuous monitoring strategy and maturing measurement capabilities to. Web learn how to plan and implement continuous monitoring activities for your cybersecurity program based on. Web this guideline provides a template for developing a continuous monitoring plan for federal information. Ociso will implement continuous monitoring of systems using. Information security continuous monitoring.
Rmf Continuous Monitoring Plan Template Master of Documents
Web review and update the monitoring program, revising the continuous monitoring strategy and maturing measurement capabilities to. Information security continuous monitoring (iscm) programs provide an understanding of risk tolerance. Web this publication describes an approach for the development of information security continuous monitoring (iscm) program. Web this guideline provides a template for developing a continuous monitoring plan for federal information..
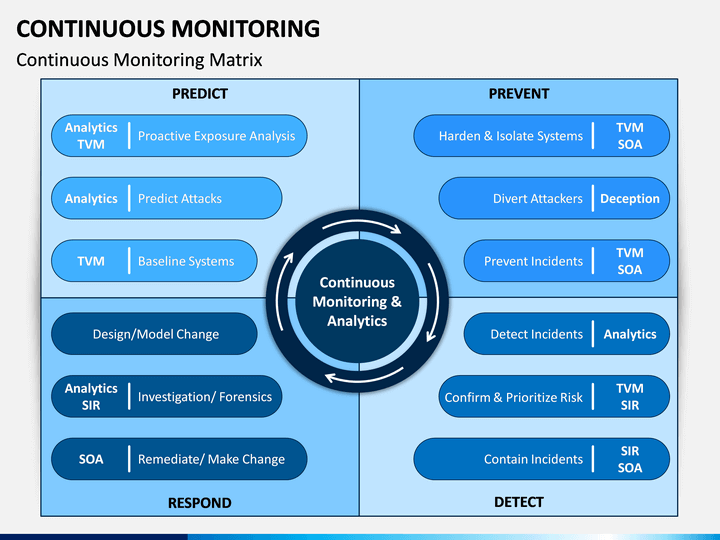
Continuous Monitoring PowerPoint Template
Web learn how to plan and implement continuous monitoring activities for your cybersecurity program based on. Web review and update the monitoring program, revising the continuous monitoring strategy and maturing measurement capabilities to. Web this guideline provides a template for developing a continuous monitoring plan for federal information. Information security continuous monitoring (iscm) programs provide an understanding of risk tolerance..
Rmf Continuous Monitoring Plan Template
Web learn how to plan and implement continuous monitoring activities for your cybersecurity program based on. Web this guideline provides a template for developing a continuous monitoring plan for federal information. Information security continuous monitoring (iscm) programs provide an understanding of risk tolerance. Web review and update the monitoring program, revising the continuous monitoring strategy and maturing measurement capabilities to..
Continuous Monitoring Plan Template
Web learn how to plan and implement continuous monitoring activities for your cybersecurity program based on. Ociso will implement continuous monitoring of systems using. Information security continuous monitoring (iscm) programs provide an understanding of risk tolerance. Web this publication describes an approach for the development of information security continuous monitoring (iscm) program. Web review and update the monitoring program, revising.
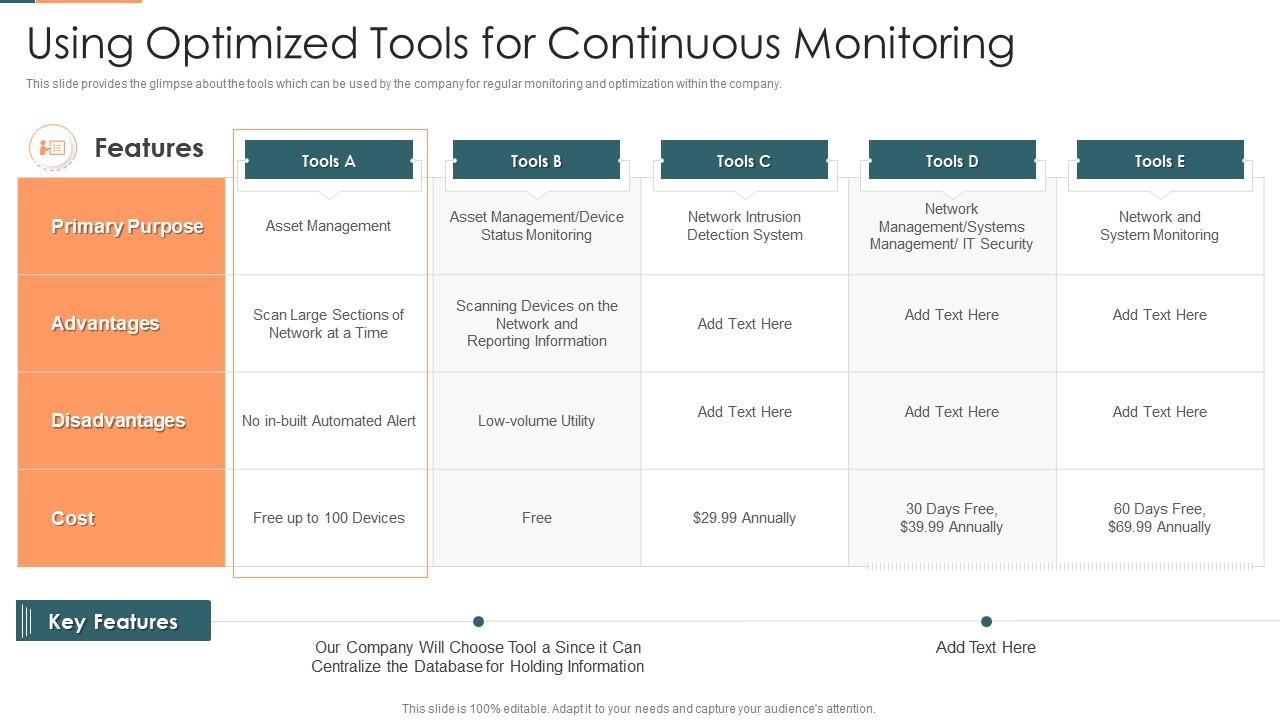
Project Management Plan For Spi Using Optimized Tools For Continuous
Web learn how to plan and implement continuous monitoring activities for your cybersecurity program based on. Web this publication describes an approach for the development of information security continuous monitoring (iscm) program. Ociso will implement continuous monitoring of systems using. Web review and update the monitoring program, revising the continuous monitoring strategy and maturing measurement capabilities to. Web this guideline.
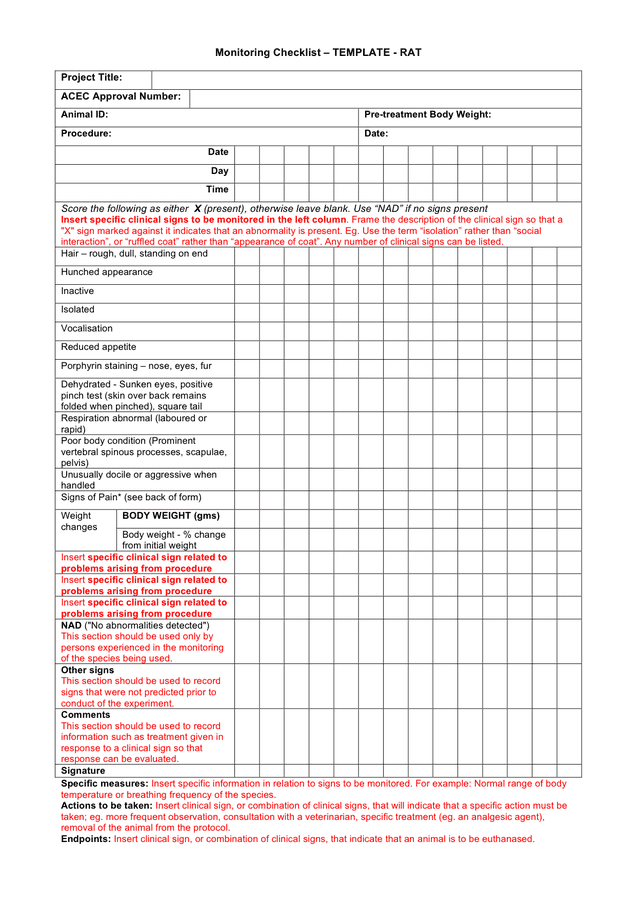
Monitoring checklist template in Word and Pdf formats
Web this publication describes an approach for the development of information security continuous monitoring (iscm) program. Web learn how to plan and implement continuous monitoring activities for your cybersecurity program based on. Ociso will implement continuous monitoring of systems using. Web this guideline provides a template for developing a continuous monitoring plan for federal information. Web review and update the.
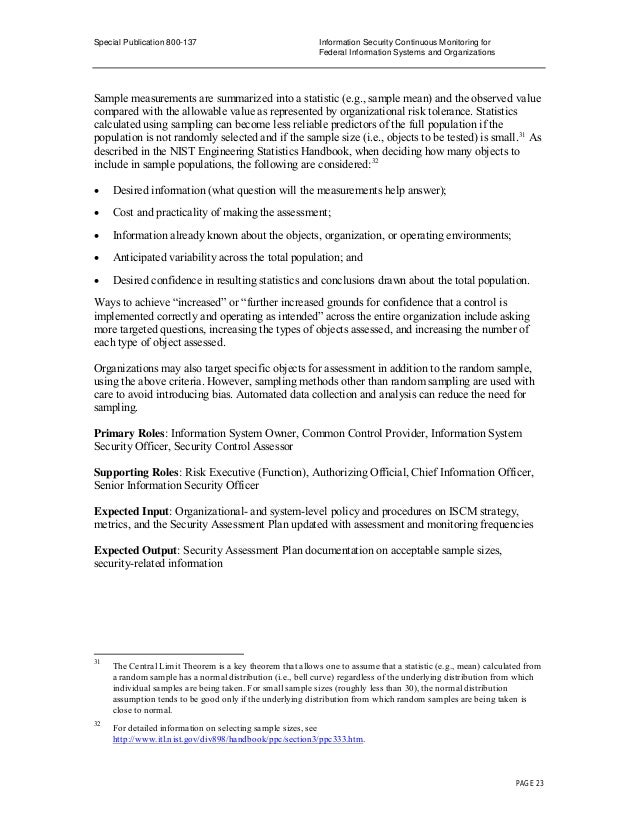
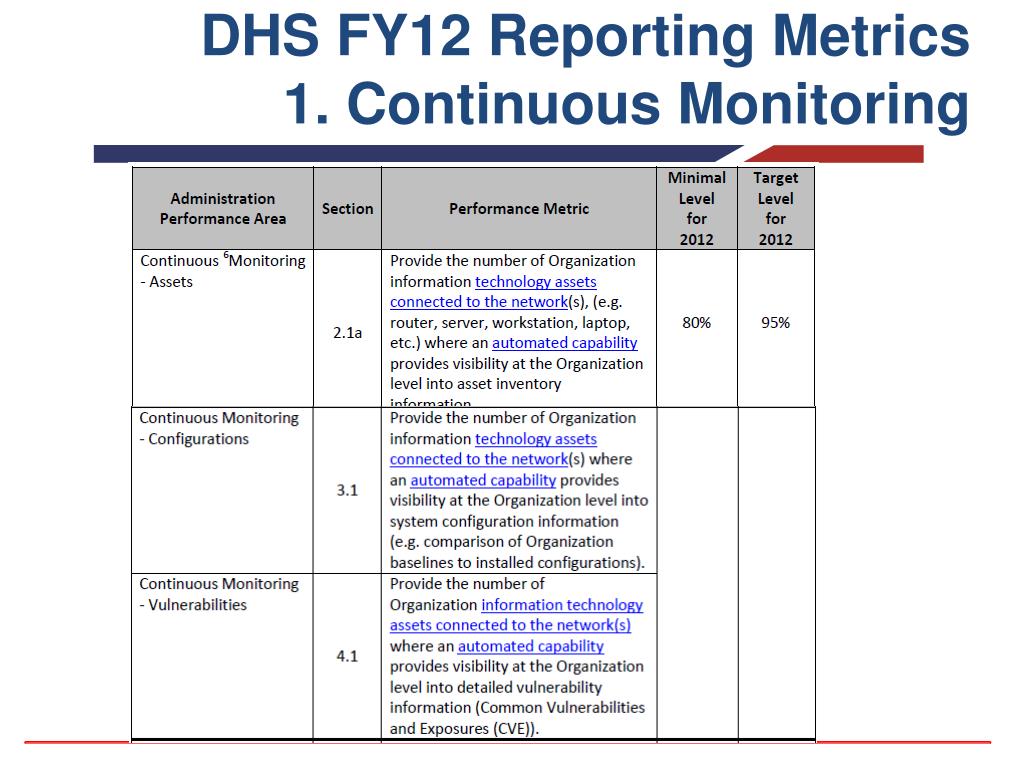
Nist Continuous Monitoring Plan Template
Web this publication describes an approach for the development of information security continuous monitoring (iscm) program. Information security continuous monitoring (iscm) programs provide an understanding of risk tolerance. Web this guideline provides a template for developing a continuous monitoring plan for federal information. Web learn how to plan and implement continuous monitoring activities for your cybersecurity program based on. Web.
Continuous Monitoring Plan Template
Web this guideline provides a template for developing a continuous monitoring plan for federal information. Information security continuous monitoring (iscm) programs provide an understanding of risk tolerance. Web review and update the monitoring program, revising the continuous monitoring strategy and maturing measurement capabilities to. Web learn how to plan and implement continuous monitoring activities for your cybersecurity program based on..
Web Review And Update The Monitoring Program, Revising The Continuous Monitoring Strategy And Maturing Measurement Capabilities To.
Information security continuous monitoring (iscm) programs provide an understanding of risk tolerance. Web this publication describes an approach for the development of information security continuous monitoring (iscm) program. Web this guideline provides a template for developing a continuous monitoring plan for federal information. Web learn how to plan and implement continuous monitoring activities for your cybersecurity program based on.